Trusted Cybersecurity for Modern Threats
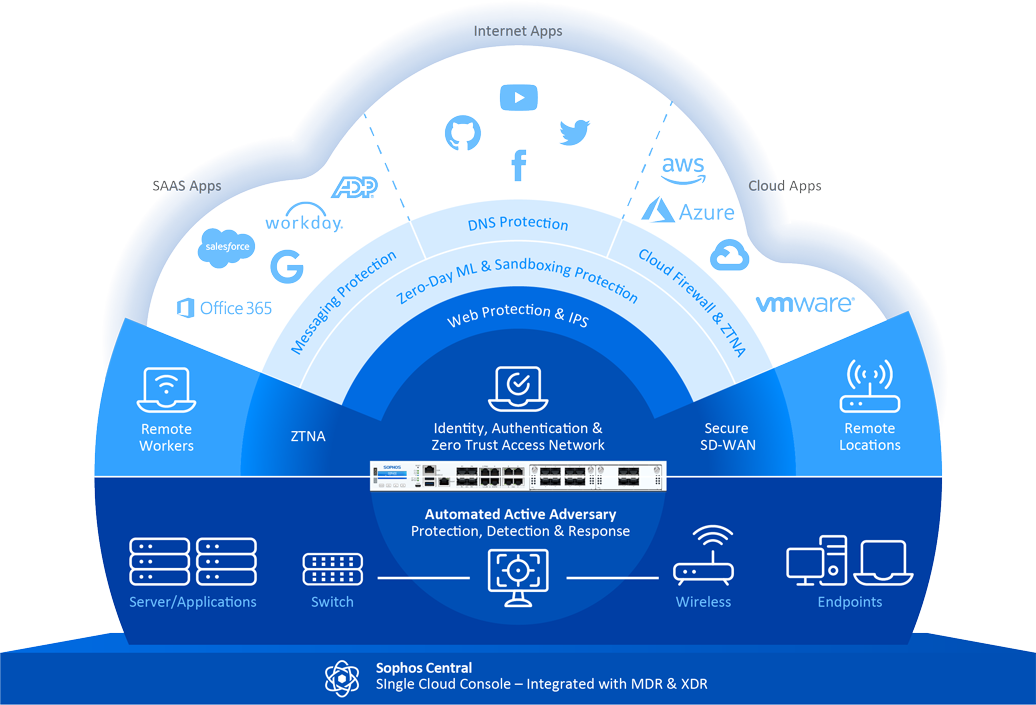
We deliver a full range of Sophos cybersecurity solutions engineered to protect your organization’s digital assets and IT infrastructure from today’s constantly changing threat landscape. By combining advanced security technologies with proven expertise, we place your security at the forefront—building a strong, reliable, and customized protection framework aligned with your business needs.
Security Built Around Your Business
- By combining advanced security technologies with proven expertise, we place your security at the forefront— building a strong, reliable, and customized protection framework aligned with your organization’s needs.
- We help you defend against ransomware, malicious files, unsafe web activity, and unknown threats—without disrupting daily operations.
Product & Environment Coverage
Centralized oversight and strong network defense
- Sophos Central
Simplify security oversight with centralized management across your entire IT ecosystem—enabling efficient monitoring, policy control, and fast response.
- Sophos Firewall & UTM 9
Strengthen network defenses with advanced firewall and Unified Threat Management solutions tailored to your infrastructure and security objectives.
Key Features & Solutions
Layered protection for endpoints, web, apps, and devices
- Endpoint Protection
Identify, eliminate, and prevent threats such as viruses, Trojans, worms, spyware, and unwanted applications using powerful antivirus capabilities supported by HIPS and Malicious Traffic Detection technologies..
- Behavior Monitoring
Protect against unknown and zero-day threats by detecting suspicious behavior through advanced monitoring powered by HIPS technology.
- Live Protection
Improve threat detection and response with real-time intelligence, instant threat lookups, and continuous updates against the latest malware..
- Web Protection
Secure web access and protect data by blocking malicious sites and scanning downloaded files for potential risks..
- Application Control
Regulate application usage across your organization by restricting unauthorized software such as VoIP tools, instant messaging platforms, file-sharing programs, and games to maintain compliance and security..
- Device Control
Strengthen endpoint protection by limiting unauthorized use of external storage devices and wireless connectivity, reducing the risk of data leakage and security breaches.